Navigating the labyrinth of digital security can be daunting. From credit card numbers to medical records, our data is increasingly guarded by complex codes. Among these, the bypass code, a crucial yet often overlooked component, serves as a vital key to unlocking otherwise inaccessible data. But how does one find this elusive bypass code easily and efficiently? This article delves into practical strategies for discovering your bypass codes.
Key Insights
- Primary insight with practical relevance: Understanding where bypass codes reside and how to access them without hassle.
- Technical consideration with clear application: The importance of digital documentation and regular audits.
- Actionable recommendation: Utilize specialized tools and digital repositories for streamlined access.
Understanding the Purpose of Bypass Codes
Bypass codes are designed to allow authorized users to bypass certain security measures, usually in emergencies or for specific tasks that require elevated access. They are particularly critical in IT environments where specific software or systems need to be accessed rapidly. For instance, in cloud computing, bypass codes can enable quick access to restricted databases. To effectively find these codes, it’s essential to understand their purpose and the contexts in which they are used.Where to Find Bypass Codes
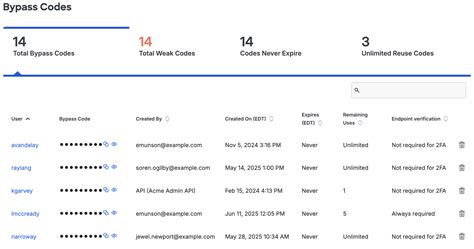
Bypass codes are often stored in secure digital or physical repositories. Firstly, ensure that you have access to official digital documentation, such as your company’s IT policy or security manual, where such codes might be listed. Secondly, regularly consult digital security dashboards or repositories if your organization uses specialized management software. Many organizations also use encrypted databases or password managers like LastPass or 1Password to store these codes securely. Additionally, maintain regular audits of these documents to ensure that no codes are misplaced or outdated.When searching for bypass codes, always follow your organization’s security protocols. Unauthorized access to these codes can lead to severe security breaches. Utilizing specialized tools can also aid in finding these codes. For example, network sniffers or protocol analyzers can be used to intercept codes being transmitted over a network.
Can bypass codes be changed frequently?
Yes, frequent changes are recommended to enhance security. Regularly updating bypass codes can significantly minimize the risk of unauthorized access.
What should I do if I can’t find my bypass code?
If you are unable to locate your bypass code, the first step should be to contact your IT security team. They have the tools and expertise to assist in recovering or generating the code.
In the landscape of digital security, bypass codes represent a critical component of emergency protocols and system access. By understanding where and how to find these codes, individuals can ensure they are prepared for any situation that requires immediate, elevated access. Always remember that the responsibility of securing and retrieving bypass codes lies within the organization’s IT governance framework. Regular audits, secure storage, and updated documentation are paramount to maintaining the integrity of your digital security protocols.